Core Of Database Integrity
Introduction
In this era of digital transformation, data has become the most valuable intangible asset for an organization or company. However, simply collecting and storing data is not enough. The biggest challenge in data management is ensuring that the data remains accurate, consistent, and secure from various threats. This is where the concept of Database Integrity plays a crucial role. Database integrity is not just a single feature, but a combination of several layers of protection[1]. These layers begin with Database Security to defend against external threats[2], followed by Privileges (access control) to prevent internal errors, and are finally safeguarded by Transaction Control Language (TCL) as a safety net against system failures[3].
Main Discussion
Database Security
Database security serves as the first line of defense. Its primary focus is to protect the database from unauthorized access, data leaks, and cyberattacks. According to ensuring data integrity requires robust security protocols, including encryption and strict authentication[1]. By implementing these methods, even if a breach occurs, the sensitive data remains unreadable to unauthorized parties, thus maintaining the availability and confidentiality of the system.
Privileges and Access Control
Once a user enters the system, the next threat often comes from the inside, such as human error or abuse of power. This is where Privileges play a role using Data Control Language (DCL)[2]. A secure system applies the Principle of Least Privilege, meaning users are only given the minimum access necessary to do their jobs. This is managed through two main commands:
- GRANT: Gives specific permissions to a user (e.g., permission only to read data).
- REVOKE: Removes access permissions from a user when they are no longer needed.
Transaction Control Language (TCL)
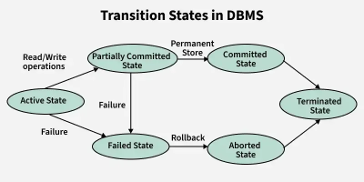
Threats to data integrity do not only come from humans but also from system failures (like power outages or server downtime). TCL ensures that a database transaction is executed entirely or not at all, following the ACID (Atomicity, Consistency, Isolation, Durability) principles[3]. The main TCL commands include:
- COMMIT: Saves all data changes permanently into the database after a transaction is 100% successful.
- ROLLBACK: Undoes all changes and returns the database to its previous safe state if an error occurs during the transaction process.
Case Study
To understand the importance of these three pillars in the real world, we can look at the ransomware attack on Bank Syariah Indonesia (BSI) in May 2023[4].
- Security Aspect: Hackers (LockBit 3.0) managed to breach BSI’s frontline defense, bypassing network security. This resulted in the theft of 1.5 TB of sensitive customer data and the locking of the banking system.
- Privileges Aspect: The attackers successfully escalated their privileges. They gained unauthorized administrative access, allowing them to move laterally through the network and access the core database. This shows why strict privilege management is crucial to contain breaches.
- TCL Aspect: During the attack and the subsequent recovery process, the bank’s core system was shut down. To ensure that no customer transactions (like ongoing fund transfers) were corrupted during the blackout, the IT team had to rely on database backups and transaction logs. They used ROLLBACK procedures to undo incomplete transactions and ensure the data returned to a consistent state (ACID principles) before safely bringing the system back online.
Conclusion
achieving true database integrity is not possible through a single security measure; it requires a comprehensive, multi-layered approach. Database Security acts as the first wall of defense against external cyber threats. Meanwhile, Privileges and access control ensure that internal users only interact with data they are authorized to handle, preventing internal errors or privilege escalation. Finally, Transaction Control Language (TCL) serves as the ultimate safety net, guaranteeing data consistency and preventing corruption during unexpected system failures.
References
[1] B. Singh, “INTERNATIONAL JOURNAL OF RESEARCH IN ELECTRONICS AND COMPUTER ENGINEERING A UNIT OF I2OR Ensuring Data Integrity and Availability with Robust Database Security Protocols,” vol. 3.
[2] M. Malik and T. Patel, “DATABASE SECURITY-ATTACKS AND CONTROL METHODS,” International Journal of Information Sciences and Techniques (IJIST), vol. 6, no. 1, 2016, doi: 10.5121/ijist.2016.6118.
[3] T. Almushaili, “Database Management Systems,” International Journal of Engineering Research and Applications www.ijera.com, vol. 12, pp. 80–86, 2022, doi: 10.9790/9622-12118086.
[4] N. Maulana, T. Laurens, H. A. Faiz, and T. Patrianti, “Manajemen Krisis PT. BSI Tbk Pasca Peretasan Data Nasabah,” INNOVATIVE: Journal Of Social Science Research, vol. 4, pp. 8244–8258, 2024.



Comments :