Implementation of Database Security and Access Control in Modern Organizations
Introduction
In the digital era, organizations rely heavily on databases to store and manage important information such as customer data, financial transactions, employee records, and operational data. Because of this dependency, database security has become a critical aspect of information technology management. Without proper protection, databases can become targets of cyberattacks, data breaches, or unauthorized access.
Database security refers to the set of tools, processes, and policies designed to protect databases from unauthorized access, misuse, or damage. It includes mechanisms such as authentication, access control, encryption, and monitoring. One important aspect of database security is the management of database privileges, which controls who can access or modify data. Additionally, Transaction Control Language (TCL) plays an essential role in ensuring data consistency and reliability during database operations.
This article discusses the implementation of database security, the importance of database privileges using commands like GRANT and REVOKE, and the role of Transaction Control Language (COMMIT, ROLLBACK, SAVEPOINT) in maintaining database integrity in real-world systems.
Main discussion
1. Database Security Implementation
Database security implementation involves multiple layers of protection to ensure that only authorized users can access or manipulate data. Organizations typically apply several security measures, such as:
- User Authentication
Authentication verifies the identity of users attempting to access the database. This is commonly done through usernames, passwords, multi-factor authentication (MFA), or digital certificates. - Access Control
Access control determines what actions users are allowed to perform in a database. This includes permissions such as reading, inserting, updating, or deleting data. - Encryption
Encryption protects sensitive data by converting it into unreadable formats unless decrypted with the proper key. Many organizations use encryption for both stored data and data in transit. - Regular Monitoring and Auditing
Monitoring systems track database activities to detect suspicious behavior, such as repeated login failures or unusual data access patterns.
These measures help organizations prevent unauthorized access and ensure that sensitive information remains secure.
2. Database Privileges and Access Control
One of the most important components of database security is privilege management. Database administrators (DBAs) control user permissions using commands such as GRANT and REVOKE.
- GRANT is used to give specific permissions to users or roles.
- REVOKE is used to remove previously granted permissions.
For example:
![]()
The command above allows user1 to read and insert data in the customers table.
If the administrator wants to remove the permission:
![]()
This command removes the ability of user1 to insert data into the table.
Proper privilege management ensures that users only have access to the data necessary for their roles. For instance:
- Employees in the finance department may access financial records.
- Customer service staff may only view customer information but not modify it.
- Database administrators have full access to manage the system.
This concept is known as the Principle of Least Privilege, which reduces security risks by limiting unnecessary access.
3. Transaction Control Language in Real Systems
Another essential aspect of database management is maintaining data consistency during transactions. This is where Transaction Control Language (TCL) becomes important.
Common TCL commands include:
- COMMIT
Saves all changes made during the transaction permanently to the database. - ROLLBACK
Cancels the transaction and restores the database to its previous state. - SAVEPOINT
Creates a temporary point within a transaction that can be rolled back to if needed.
Example scenario:
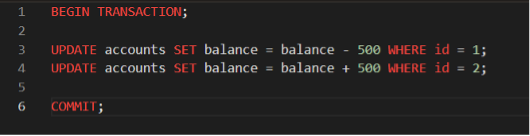
In this example, money is transferred from one account to another. If an error occurs before the COMMIT, the system can use ROLLBACK to prevent inconsistent data, ensuring that the transfer either completes fully or not at all.
This mechanism is essential in systems such as:
- Banking systems
- E-commerce platforms
- Reservation systems
Without TCL commands, partial transactions could lead to serious data inconsistencies.
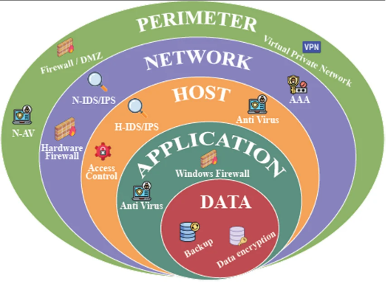
Database Security Architecture Diagram
Below is a simple illustration of how database security layers work in an organization.
Explanation of the diagram:
- Users access the system through applications.
- Authentication verifies the user identity.
- Access control determines permissions.
- The database stores the protected data.
Conclusion
Database security is a crucial component of modern information systems. Organizations must protect their databases from unauthorized access, data leaks, and cyberattacks. Implementing strong security measures such as authentication, encryption, and monitoring helps safeguard sensitive information.
In addition, managing database privileges using commands like GRANT and REVOKE ensures that users only have access to the data necessary for their roles. This reduces the risk of misuse or accidental data modification.
Furthermore, Transaction Control Language (TCL) commands such as COMMIT, ROLLBACK, and SAVEPOINT help maintain data consistency and integrity during database transactions. These mechanisms are essential in real-world systems where data accuracy is critical.
Overall, combining proper security implementation, controlled access privileges, and reliable transaction management enables organizations to maintain secure and trustworthy database systems
References
Connolly, T., & Begg, C. (2015). Database Systems: A Practical Approach to Design, Implementation, and Management. Pearson Education.
Silberschatz, A., Korth, H. F., & Sudarshan, S. (2019). Database System Concepts. McGraw-Hill Education.
Oracle. (2023). Database Security Guide. Retrieved from https://docs.oracle.com
Microsoft. (2023). SQL Server Security Best Practices. Retrieved from https://learn.microsoft.com



Comments :