Information System Security
Information Security Management System is a system management Where aiming For protect information from all form threat and also risks that can occur happened . This information system security functioning For ensure confidentiality , integrity and availability information in a existing organizations . This is can help a company and also organization For fulfil condition laws and regulations related security information , besides that’s information system security also useful for increase trust from the stakeholders interest like customers , partners business , and also regulators .
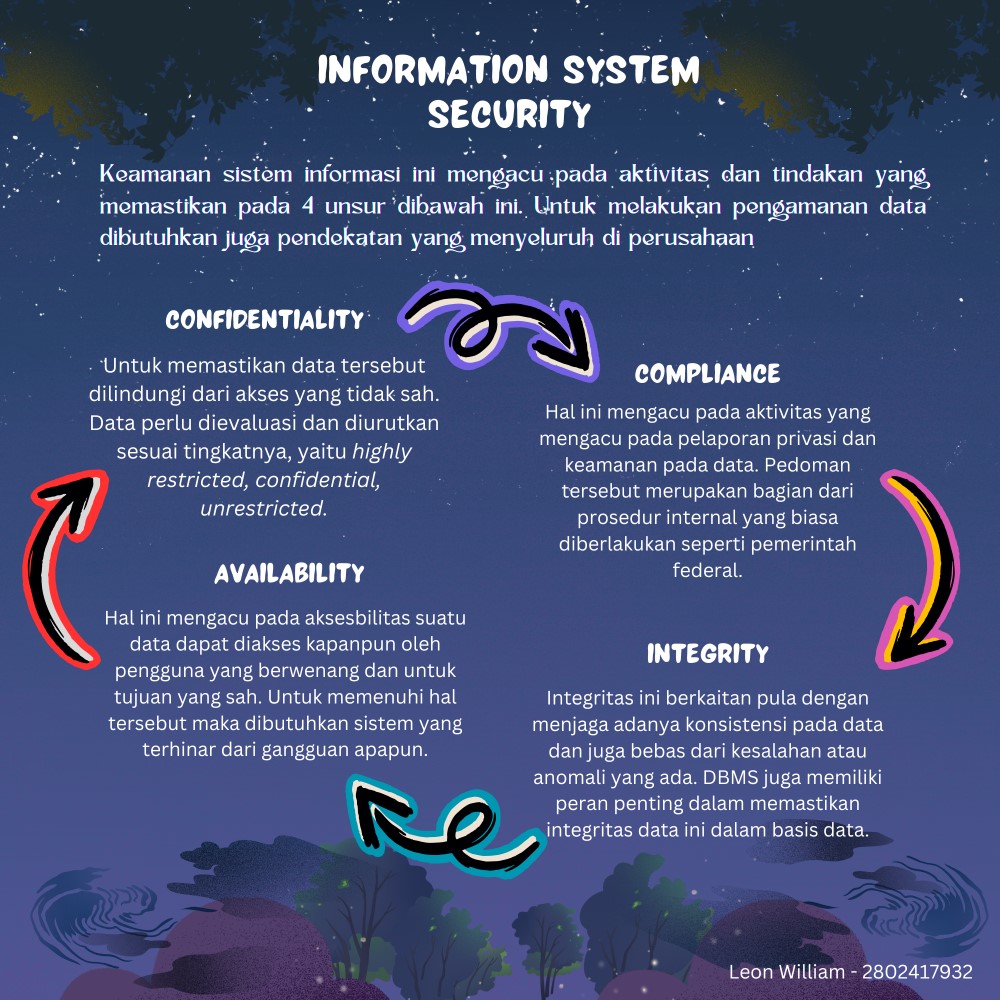
Security information This useful For protect a valuable asset from existence loss , misuse , or the damage that exists . This is aiming For guard sustainability a business , minimize existing risks or Possible happens , and is also useful For maximize a the benefits that can be obtained from investment said . For do effort Handling or control on the side security information this , then required existence a number of aspects that need to be considered under consideration moreover previously , such as Confidentiality, Compliance, Integrity, and Availability.
• Confidentiality
On the aspect this , moment want to protect information We need For give limitation access to those who are allowed For can see it . So that only Can accessed by authorized persons so that sensitive information or confidential That will still protected from the party that does not desired .
• Compliance
On the aspect This own activity Where management technology information in accordance with standards applicable in the environment or specific institution , thing This covers about issues specifics that require company For apply defined infrastructure use For protect a data. This is beneficial For protect information customers , reduce risk laws and fines , increasing efficiency operational , improve reputation company , and also minimize operational risks .
• Integrity
Integrity This related with authenticity and also truth in the information , which means a information must still intact and not experience changes that are not legitimate during storage , delivery , and processing . Efforts For guard a integrity information This involving action For prevent modification or manipulation that is not valid . However integrity This Can just is lost in a way No on purpose like when someone in authority That make change in a way No on purpose with delete file or enter information that is not appropriate .
• Availability
On the aspect This can it is said that a information can accessible and can modified by anyone who has given authority For do it in term the right time . Systems and infrastructure This need designed and managed such that appearance so that Can respond request access information with fast and also without existence significant disruption .
Based on fourth aspect said , aspects Confidentiality is the one that often happens considered as the most important component . Due to confidentiality is the crucial thing Because when We lost matter the can result in serious consequences . However other aspects also have role importance each because of with ensure that every component be noticed with Good in accordance with need specific and level risks faced .
Reference:
Purwanti , Henny (2023). Information Security Management System (ISMS) https://www.djkn.kemenkeu.go.id/kanwil-jakarta/baca-article/16304/InformationSecurity-Management-System-ISMS.html Dave Bourgeois, David T. Bourgeois (2014) https://pressbooks.pub/bus206/chapter/chapter-6-information-systems-security/
Pilo , Rani (2024) https://aplikas.com/blog/cia-triad/
https: / /amt-it.com/blog/it-compliance-dengan/#Understanding_IT_Compliance
Editor : Edi Purnomo Putra



Comments :